Save time and money with Google Workspace automate solutions for onboarding and offboarding
Automate your core business processes with bespoke workflows and dynamic user groups.
Request a demo



Simplify IT onboarding and offboarding
CloudM Automate enables you to automate these manual, repetitive tasks to avoid mistakes, save time and control costs.
“We’re utilizing Automate for all of our employee offboarding across the Google Workspace, meaning that we now have a graceful and consistent methodology for all business leavers.”
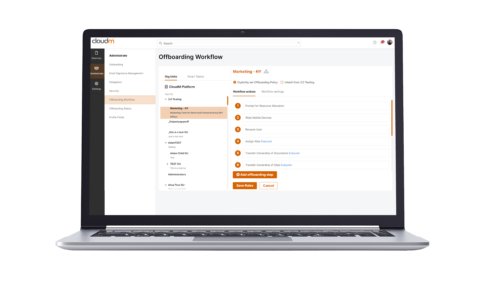
Offboard staff in minutes
CloudM Automate comes with over 35 customizable workflow steps that help you offboard staff in minutes, and its dynamic groups offer complete flexibility.
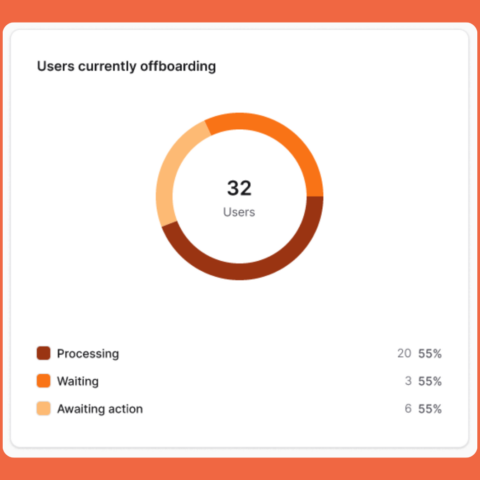
Information at your fingertips
Gain instant insights into the status of your automation workflows with the Automate dashboard. Key features include:
- At-a-glance status: Easily monitor the progress and health of your onboarding and offboarding workflows.
- Actionable data points: Directly address issues like failed offboardings from the dashboard view.
- Data export: Export your dashboard data to PDF for easy reporting and sharing.
- Interactive tooltips: Access contextual information and guidance through informative tooltips
Boost productivity with connectors
Use out-of-the-box connectors to create workflows involving systems such as Slack, Dropbox and BambooHR.

Security at the core
Your data security is our priority.
Book a call with our automation specialists today